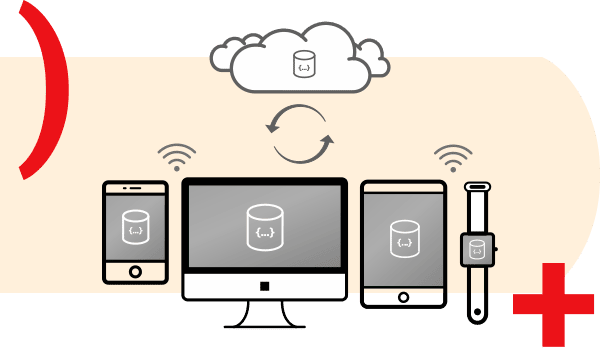
Cloud-to-edge sync
Securely sync mobile apps from cloud to edge. Sync Gateway provides data security between your web, mobile, and IoT apps running Couchbase Lite and your backend Couchbase Server, Couchbase Edge Server, or Couchbase Capella deployments.
Built-in data integration APIs
Use secure RESTful APIs for accessing and managing data over the web and webhooks to integrate with external web clients, data stores, and services.
Robust security
Enforce read and write access from the scopes and collections level down to individual user and role. Admin REST API enforces authentication and role-based access control by default. Take advantage of third-party Open ID Connect providers or bring in custom providers.

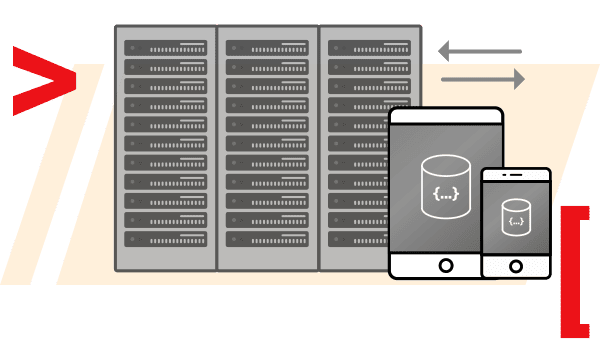
Elastically scalable in real time
Vertically and horizontally scale Sync Gateway nodes to handle changes in capacity demands. Apply tunable read and write scaling options to meet performance demands.







