This blog was originally posted on Roi Katz’s personal blog site. Please click here to find the original post.
Hi all!
So you want to authenticate users access to Couchbase through your Active Directory LDAP service.
Couchbase has that ability.
You can actually map every user to one of three access permissions levels (as for v4.1)
- Full Admin
- Read Only
- No access
I assume the following:
- You already have an Active Directory up and running
If not, please refer to here or here for setup instructions.
- You already have Couchbase already installed (on a Linux Distro)
If not, please refer to those guides: RHEL or Debian
As for v4.1 of Couchbase, only the Linux distros support the LDAP, it’s not available on Windows nor MacOS.
My setup here is an Azure Windows server 2012 R2 VM with Active Directory and a local Ubuntu 14.04.3 LTS VM with Couchbase v4.1 installed.
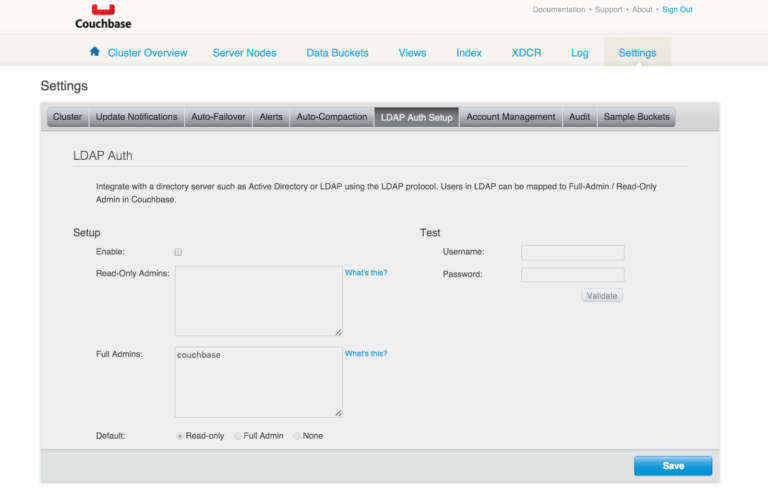
In the setting of your Linux Couchbase you will find a tab called LDAP Auth Setup
To fully understand how the LDAP authentication works with Couchbase, please read Couchbase’s documentation.
So first thing first, install the saslauthd
Pay attention if you are using RHEL or Ubutntu, paths and instructions are a bit different.
TL;DR version in Ubuntu
- sudo apt-get update
- sudo apt-get install sasl2-bin
- sudo nano /etc/default/saslauthd
- Change START=yes, MECHANISMS=”ldap”
- Save and quit (ctrl+x)
- switch to sudo (sudo -u)
- change permission for /var/run/saslauthd and /var/run/saslauthd/mux to 755 so couchbase user can access them.
- cd to /etc folder
- if saslauthd.conf does not exist – touch it and add 755 permissions.
- configure the file as follows:
|
1 2 3 4 5 6 7 8 9 10 11 |
ldap_servers: ldap://yourmachineaddress:389 ldap_search_base: dc=couchbase,dc=org ldap_filter: (sAMAccountName=%u) ldap_bind_dn: CN=[admin user],CN=Users,DC=couchbase,DC=org ldap_password: [admin password] ldap_auth_method: bind ldap_version: 3 ldap_use_sasl: no ldap_restart: yes ldap_deref: no ldap_start_tls: no |
ldap_servers is your AD server
ldap_search_base is on what domain you would like to search users (here it’s couchbase.org on AD)
ldap_filter is what you want to return
ldap_bind_dn is a user with admin privileges permissions who can search the AD user tree.
ldap_password the admin user password
- Open Active Directory ports for LDAP, 389 (TCP+UDP), 3268,3269, 636 (UDP)
- You can test your active directory connection with JXplorer
- Restart your salsauthd service – sudo service saslauthd restart
- Test it! – sudo -u couchbase /usr/sbin/testsaslauthd -u -p mypassword -f /var/run/saslauthd/mux
- if you have permissions and set it all up as above you should get a success message. the username and the password here are the ones you want to check, not the ldap admin.
Now let’s use it on the Couchbase console!
- Login to your cluster management console and hit settings -> LDAP Auth setup.
- Enable LDAP
- Choose your default behavior – if you don’t specify the username anywhere
- Write down some users or groups in each box
- Hit save
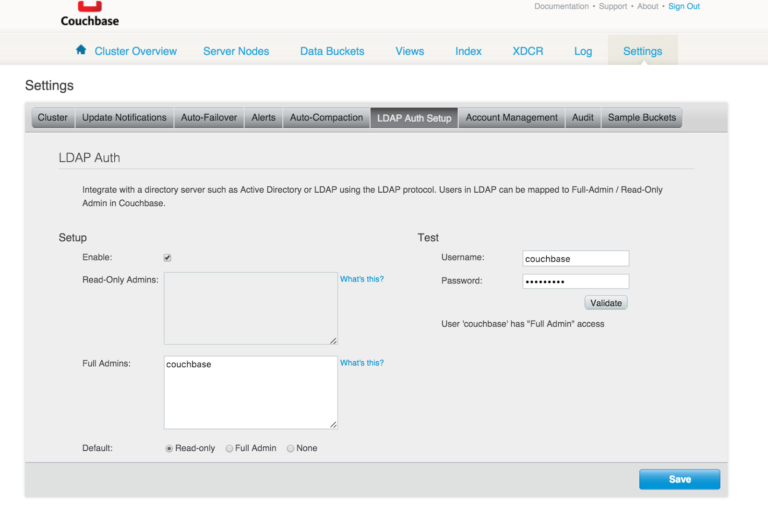
- Test it (on the right)
- If everything is ok – you should get something like “user ‘x’ has ‘Full Admin’ access because I’ve listed that user under the Full Admin.
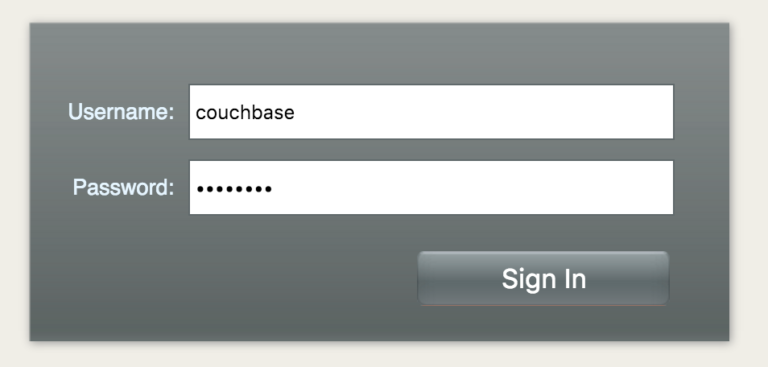
- now sign out and try logging in with the Active Directory Credentials.
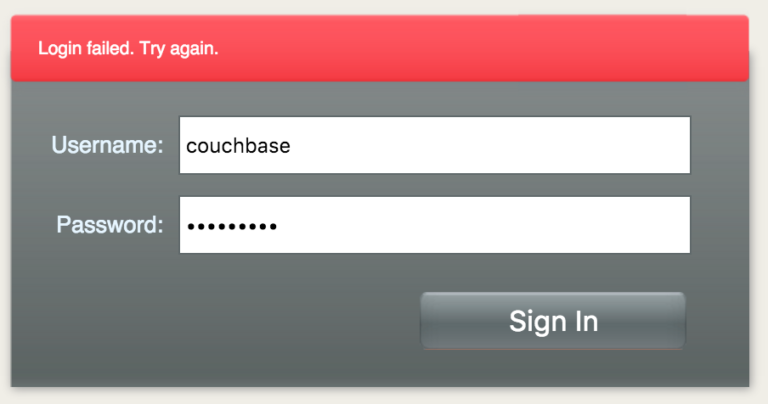
If I will get the password wrong – I won’t be able to access, as expected.
In case you AD server is unreachable, you would still be able to log in through your regular Couchbase accounts.
Thats all! Hope you enjoyed.
Roi.
Could we have an updated version of this for Version 5. We have just set this up on a RedHat cluster and the “LDAP Auth Setup” tab no longer exists.
In the works.
In the meanwhile use the couchbase-cli ldap-setting with ldap-enabled 1 flag to enable ldap.