Category: Security

Securely Storing Password Data in Couchbase with Golang and BCrypt
Learn how to use BCrypt in a Golang application to hash sensitive information like passwords before storing them in a NoSQL database like Couchbase.
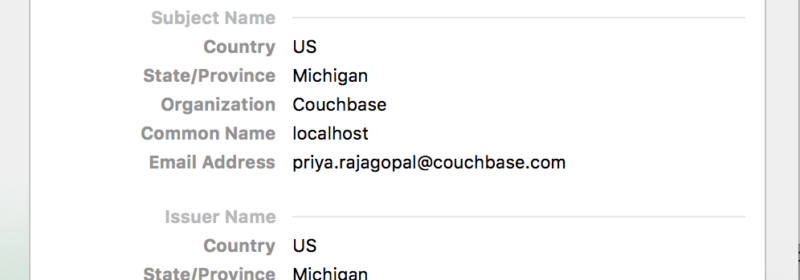
Certificate Pinning in your Couchbase Mobile iOS App
The SSL/TLS protocol relies on a PKI mechanism that has certain drawbacks.Certificate pinning is a technique that is used by applications to alleviate this.
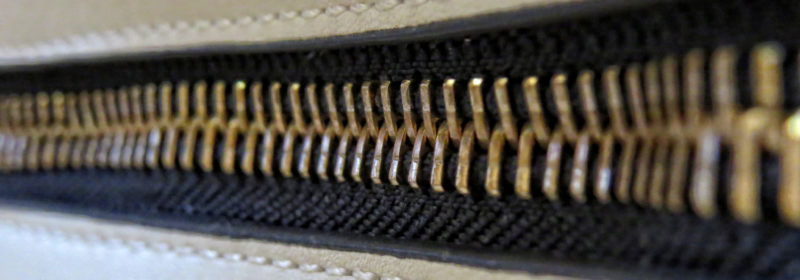
Putting a Zipper on the Back of the Hospital Gown
Last week, security firm Appthority published a report titled HospitalGown: The Backend Exposure Putting Enterprise Data at Risk, which highlighted newly-discovered vulnerabilities between mobile apps and insecure backend databases containing enterprise data. The vulnerability is caused not by code in...

Authentication and Authorization with RBAC in .NET
Examples of using the Couchbase .NET SDK with the new authentication and authorization features of Couchbase Server 5.0

Improved SDK Authentication Methods – Couchbase 5.0
Couchbase 5.0 delivers new authentication security features that require minor changes to your client connection code. This post tells you how to do it!

Authorization & Authentication with RBAC (Part 2)
Authentication and authorization are important to Couchbase. I'd like to go into more detail now that the April Couchbase 5.0 Developer Build is available.

Authentication and Authorization with RBAC
In March's developer build, you can start to see some major changes to authentication and authorization within RBAC coming to Couchbase Server.

Announcing Couchbase Server 4.6 – What’s New and Improved
Couchbase Server 4.6 provides the availability, scalability, performance, and security that enterprises require for their mission-critical applications.

Introducing Role-Based Access Control in Couchbase Server 4.5
Over the years, it has been drilled into me to use “Least Privilege” access whenever and however possible. This specially applies to administrators – they manage important IT infrastructure components like NoSQL databases, and have the liberty to use all...

Introducing Couchbase Server 4.6.0 Developer Preview
Today, we’re very excited to announce the availability of Couchbase Server 4.6.0 DP. This is an early developer release that comes with some exciting capabilities for cross datacenter replication, security, query, tools, and powerful full text search capability. The Developer...

Skipping default bucket creation
Some days ago I made the following search: “databases unprotected”. It is really incredible the number of databases deployed without authentication. Most of them are just test databases published on the internet, but others are exposing sensitive data. (Image Licensed through...

Configuring IPsec for a Couchbase Cluster
Introduction Some Couchbase deployments require secure communications between nodes across the network, this could be due to reasons like data governance policies or regulatory compliance. Internet Protocol Security (IPsec) is a protocol suite for secure Internet Protocol (IP) communications by...
Top Posts
- Data Modeling Explained: Conceptual, Physical, Logical
- What are Embedding Models? An Overview
- Couchbase Mobile Delivers Major Advancements for Building Offline...
- Data Analysis Methods: Qualitative vs. Quantitative Techniques
- Application Development Life Cycle (Phases and Management Models)
- What Is Data Analysis? Types, Methods, and Tools for Research
- Couchbase 8.0: Unified Data Platform for Hyperscale AI Applicatio...
- How to Model Data: A Guide To JSON Data Modeling
- What are Vector Embeddings?