As more and more organizations adopt cloud computing, the use of multi-cloud environments is becoming increasingly common. However, with this approach comes the need for robust multi-cloud security strategies to effectively secure and protect data and resources across multiple cloud environments.
This article provides an overview of potential threats you may face when using multiple cloud service providers, best practices for securing multi-cloud environments, and challenges you may encounter when implementing multi-cloud security strategies. We’ll also provide guidance on developing a solid multi-cloud security strategy that can help you protect your data and resources in a multi-cloud environment.
By the end of this article, you will better understand what multi-cloud security entails, its potential risks and challenges, and the best practices for developing a solid multi-cloud security strategy.
What is Multi-Cloud Security?
Cloud security is a critical aspect of modern-day cloud computing. As businesses increasingly adopt multi-cloud architectures to leverage the benefits of various cloud providers, the complexity of securing these environments increases exponentially.
Multi-cloud security refers to the policies, procedures, and technologies implemented to protect data, applications, and infrastructure across multiple cloud service providers. It ensures the confidentiality, integrity, and availability of resources in multi-cloud environments while maintaining compliance with relevant regulatory requirements.
The first thing to know about multi-cloud security is that each cloud provider has a unique set of security controls, compliance requirements, and threat landscape. Multi-cloud security requires a comprehensive approach that considers the security of each cloud provider and the interactions between them. This approach involves identifying and assessing the risks associated with each cloud platform, implementing security controls to mitigate those risks, and monitoring the environment for potential security threats.
Multi-cloud security also involves integrating security tools and services across multiple cloud platforms. It can include deploying multi cloud security solutions such as firewalls, intrusion detection and prevention systems, and security information and event management (SIEM) tools. It is also essential to establish clear security policies and procedures for managing access, data protection, and incident response across all cloud platforms.
Now that you understand what multi-cloud security is, let’s explore some of the most common threats you may face in a multi-cloud environment.
Multi-Cloud Security Threats
When designing a comprehensive security plan for a multi-cloud environment, you need to consider and identify the various security threats that could impact the infrastructure. Multi-cloud security is a complex process due to the evolving nature of the threat landscape, which involves sophisticated and frequent cyber-attacks that exploit vulnerabilities in the infrastructure.
Here are some common multi-cloud security threats you should consider when designing a security plan for your multi-cloud environment:
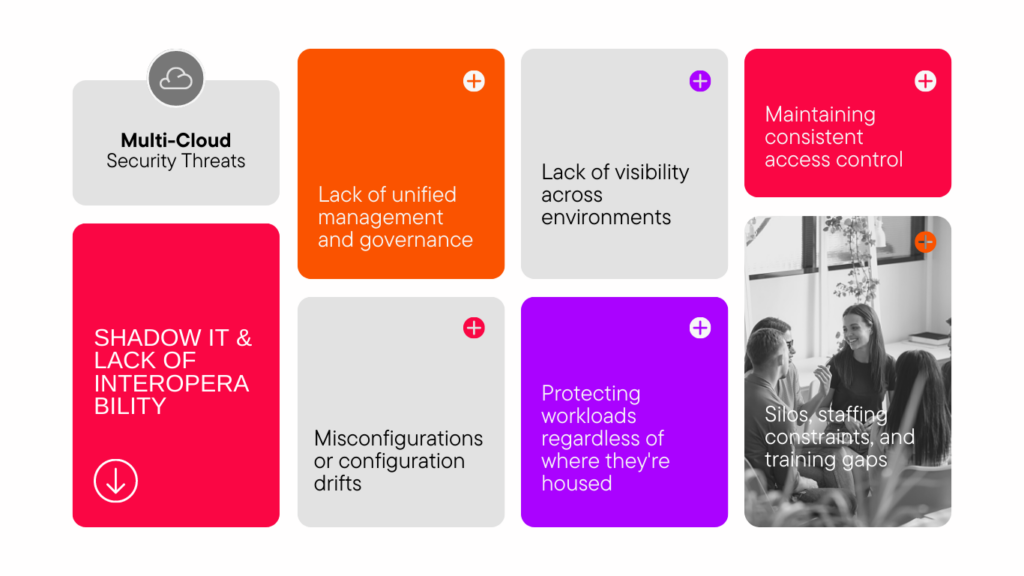
Lack of unified management and governance: Managing security policies, access control, and monitoring across multiple cloud environments can be challenging, especially when there is no unified governance in place.
Silos, staffing constraints, and training gaps: Inconsistencies in security policies and procedures across different cloud environments may arise due to silos, staffing constraints, and training gaps. Such inconsistencies can result in exposure to cyber-attacks and make it difficult to respond to security incidents effectively.
Protecting workloads regardless of where they’re housed: It’s essential to ensure that your workloads are protected, regardless of where they’re housed. To do this, you must implement consistent security policies and access controls across all cloud environments.
Lack of interoperability: Different cloud providers use different APIs and protocols, which can lead to interoperability issues. Without proper integration, security policies may not be enforced consistently across all environments.
Misconfigurations or configuration drifts: Misconfigurations or configuration drifts can occur when changes are made to one cloud environment but not replicated across all environments. It can lead to security vulnerabilities and can make it challenging to maintain a consistent security posture challenging.
Lack of visibility across environments: Detecting security incidents across all cloud environments can be challenging without proper monitoring and visibility tools. It can lead to delayed responses and increased damage.
Maintaining consistent access controls: It’s important to ensure that access controls are consistent across all cloud environments. Consistency means enforcing strong authentication and authorization policies and regularly reviewing access permissions.
Shadow IT: Shadow IT can occur when business units use cloud services without IT approval. It can lead to security vulnerabilities and make it challenging to maintain a consistent security posture across all environments.
Developing a Multi-Cloud Security Strategy
Developing a comprehensive multi-cloud security strategy requires a deep understanding of the potential threats and risks a multi-cloud environment poses. It also involves identifying the most critical assets and data that require protection and implementing the appropriate security controls to safeguard them.
Here are some key elements to consider when developing a multi-cloud security strategy:
-
- Identify Critical Assets and Data: You should start by identifying critical assets and data that require protection. Critical assets include sensitive customer information, financial data, intellectual property, and other proprietary information that, if compromised, could cause significant damage to your organization.
- Assess Risks and Threats: Once you have identified critical assets, assess the potential risks and threats to those assets. Assessing risks includes considering the threat landscape, including insider threats, external threats, and supply chain attacks, and identifying vulnerabilities in your infrastructure and applications.
- Choose a Security Framework: Choose a security framework that aligns with your organization’s goals and regulatory compliance requirements. Popular frameworks include the National Institute of Standards and Technology (NIST) Cybersecurity Framework, the Payment Card Industry Data Security Standard (PCI DSS), and the ISO 27001.
- Implement Security Controls: Implement security controls that align with your chosen framework to mitigate identified risks and threats. These security controls may include identity and access management, network segmentation, encryption, data loss prevention, and security monitoring.
- Monitor and Test: Regularly monitor and test your multi-cloud security strategy to ensure it is effective and up-to-date. Monitoring and testing include conducting regular vulnerability assessments, penetration testing, and security audits.
- Plan for Incident Response: Develop an incident response plan that outlines the steps to take in the event of a security incident. Your plan should include identifying a response team, defining roles and responsibilities, and establishing communication channels.
- Regularly Test Your Security: Test your security strategy regularly to identify vulnerabilities and assess the effectiveness of your security controls. Conduct penetration testing and vulnerability assessments to identify weaknesses in your multi-cloud environment.
- Stay Up-to-Date with Security Trends: Stay up-to-date with the latest security trends and threats in the industry. Participate in security communities, attend conferences, and read industry reports to stay informed and adjust your strategy accordingly.
Multi-Cloud Security Best Practices
In order to ensure the security of your multi-cloud environment, it is essential to follow best practices that can mitigate the risks associated with a complex and distributed system. Here are some of the best practices for multi-cloud security:
Use a unified management and governance platform: By using a unified management and governance platform, you can enforce consistent policies across all cloud providers, simplify compliance reporting, and reduce the risk of misconfigurations.
Implement a comprehensive identity and access management (IAM) strategy: A comprehensive IAM strategy includes role-based access controls, multi-factor authentication, and centralized management of user accounts.
Use encryption for data at rest and in transit: Encryption is a critical component of multi-cloud security, as it protects sensitive data from unauthorized access.
Monitor and analyze logs and events: By monitoring logs and events, you can detect security incidents and respond quickly to mitigate risks.
Regularly conduct vulnerability assessments and automated penetration testing: Vulnerability assessments and penetration testing are critical components of multi-cloud security, as they help identify potential vulnerabilities in your infrastructure and applications.
Adhering to best practices involves deliberation and patience when selecting multi-cloud security solutions. Thoroughly vet each solution, and be sure not to rush into a decision until you’ve gathered all the necessary information.
Multi-Cloud Security Challenges
As with any technological innovation, multi-cloud security has its share of challenges. Here are some common challenges that you may face when implementing multi-cloud security:
Complexity: Multi-cloud security can be complex, especially when different cloud providers have their own security protocols and policies. It can make it difficult to maintain a comprehensive view of your security posture across all clouds.
Integration: Integration is a major challenge when it comes to multi-cloud security. You need to ensure that your security tools and processes integrate with each cloud provider’s APIs to monitor, detect, and respond to security threats.
Compliance: With multiple cloud providers, you may find it challenging to maintain compliance with different regulatory requirements. It can complicate handling sensitive data such as personally identifiable information (PII) or payment card information.
Skills gap: Implementing a multi-cloud security strategy requires specialized skills and knowledge of different cloud providers’ security protocols. You may not have in-house employees with this expertise, which can lead to challenges in developing and maintaining a robust security posture.
Cost: Managing security across multiple clouds can be costly. You may need to invest in additional tools and resources to manage security across multiple clouds, which can add to overall IT costs.
With the increasing adoption of multi-cloud security architectures, it’s important to be aware of the potential risks and challenges of securing multiple cloud platforms. The key to effective multi-cloud security is to adopt a comprehensive approach that considers each cloud provider’s unique security controls, compliance requirements, and threat landscapes.
Adopting this approach involves identifying and assessing the risks, implementing security controls, and monitoring the environment for potential security threats. To safeguard data and infrastructure from multi-cloud security threats, you must establish clear security policies and procedures, integrate security tools and services across all cloud platforms, and maintain consistent access controls.
Conclusion
Multi-cloud security is an essential aspect of modern-day cloud computing. As more businesses adopt multi-cloud architectures to leverage the benefits of various cloud providers, the complexity of securing these environments increases.
Multi-cloud security requires a strategy that considers the unique set of security controls, compliance requirements, and threat landscape of each cloud provider. It is also essential to identify and assess the risks associated with each cloud platform, implement security controls to mitigate them, and monitor the environment for any potential security threats.
As discussed, a robust multi-cloud security strategy must also address the challenges posed by multi-cloud security, such as the lack of unified management and governance, silos, staffing constraints, and training gaps. By adopting the best practices for developing a solid multi-cloud security strategy and mitigating the potential security threats discussed, businesses can ensure the confidentiality, integrity, and availability of resources in multi-cloud environments while maintaining compliance with relevant regulatory requirements.
To learn more about multi-cloud and cloud computing, check out this resource and read about our cloud database platform, Capella, here.