Category: Security

Authentication With X.509 Certificates
What is certificate-based authentication? It is built by leveraging the X.509 public key infrastructure (PKI) standard to secure authentication at scale.

Couchbase Server 5.5: Log Redaction
Learn what is Log Redaction which is a new feature of Couchbase Server 5.5. How does it work and how to enable the Log Redaction.

Announcing Couchbase Server 5.5 – Developer Build
Announcing Couchbase Server 5.5 Developer Build It is my pleasure to share this early preview of Couchbase Server 5.5 features – there are some very exciting improvements coming and this Developer Build (DB) highlights several of them. There are many...

GDPR: Businesses must focus on digital transformation, not just tick-box compliance
Learn more about GDPR and how to trigger a response from the business.Why it is important and why businesses should focus on digital transformation.

Speculative Execution Processor Vulnerabilities – Performance Impact Analysis
Last week, we published a blog with recommendation on securing Couchbase data platform in response to industry-wide security vulnerabilities. We continued to analyze the potential performance impact caused by the patched OS binaries and this blog post captures the detailed evaluation. As...

Speculative Execution Vulnerabilities – Meltdown & Spectre
How do processor/OS vulnerabilities like Meltdown & Spectre affect modern systems and may affect user-space applications like Couchbase, etc.
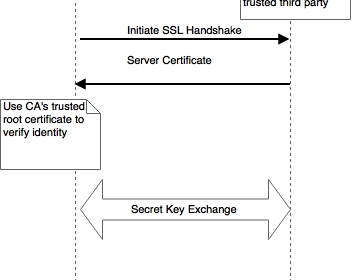
Certificate Pinning in Android with Couchbase Mobile
Certificate pinning is a technique used to “pin” a host to it’s public key certificate.Post discusses how to do this in a Couchbase Lite enabled Android app

Secure Your NoSQL Data with Couchbase Role-Based Access Control
Learn how to define an access control configuration in Couchbase Server to protect your cluster, buckets, and data from being accessed without permission.

Announcing Couchbase Mobile 1.5
With Couchbase Mobile 1.5 you can extend an existing Couchbase Server deployment to connect with remote edge devices that are disconnected or connected.

Announcing Couchbase Server 5.0
Couchbase Server 5.0 is available now. With this release check out three major pillars with many large enhancements in each area.

Using Role-Based Access Control in N1QL
Walk through the main functionality of role-based access control (RBAC) in Couchbase. These exercises will let you try out the new features for yourself.

CURL Comes to N1QL: Querying External JSON Data
Check out the examples which show using the CURL function, N1QL users can now interact with any external API’s that return results in JSON format.
Top Posts
- Data Modeling Explained: Conceptual, Physical, Logical
- What are Embedding Models? An Overview
- Data Analysis Methods: Qualitative vs. Quantitative Techniques
- A Breakdown of Graph RAG vs. Vector RAG
- What are Vector Embeddings?
- Application Development Life Cycle (Phases and Management Models)
- What Is Data Analysis? Types, Methods, and Tools for Research
- Semantic Search vs. Keyword Search: What’s the Difference?
- Six Types of Data Models (With Examples)