
Documentation
Couchbase Server has a full suite of data security features for authentication, authorization, encryption, enterprise key management, and auditing to meet the needs of your most critical and sensitive database workloads.
Use centrally managed controls to keep data access aligned with your shifting business priorities.
Ensure your database meets your security needs as it scales.
Integrate Couchbase’s logging data and monitoring capabilities into your daily tools.
Couchbase Capella DBaaS delivers SOC 2, HIPAA, GDPR, PCI DSS, and ISO 27001.
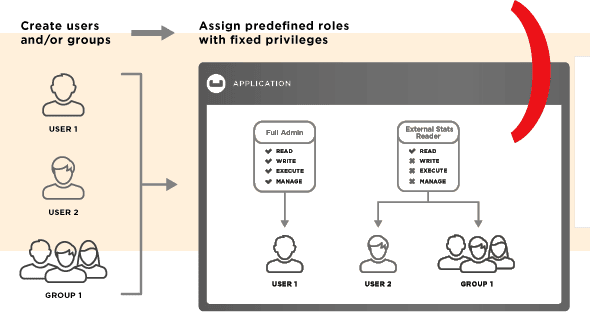
Couchbase Server’s secure authentication protocols and role-based access controls (RBAC) let you align groups of users in a centrally managed system to control access and permissions. Enforce strong password policies and manage local accounts to further harden access. Administrators can use granular controls to minimize risk exposure.
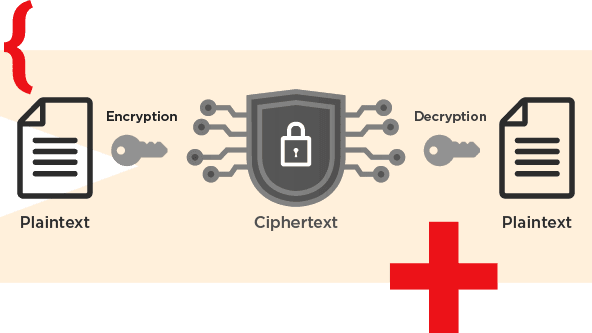
Multiple levels of high-strength encryption protect data at rest natively, in transit, and in process to meet a wide range of regulatory requirements. Integrate with your enterprise key management infrastructure via KMIP to centralize control over encryption keys. Our key security features are available across the entire Couchbase Server set of services to support key-value, transaction, and analytic use cases both on premises and when using our Capella DBaaS.
Collect and integrate security-related information from Couchbase Server into a corporate SIEM system using a secure REST API and standard JSON data formats. Monitor key system configuration changes and respond to incidents or perform forensic analysis.
