Category: Best Practices and Tutorials

Using Fluent Bit for Log Forwarding & Processing with Couchbase Server
Find out how to use Fluent Bit for log forwarding and processing with Couchbase Server, along with background on the various components involved.
![OAuth 2.0 & OIDC Fundamentals for Authentication & Authorization [Part 1 of 3]](https://www.couchbase.com/blog/wp-content/uploads/sites/1/2021/06/feature-800x280.png)
OAuth 2.0 & OIDC Fundamentals for Authentication & Authorization [Part 1 of 3]
Discover how to implement implicit and authorization code flows for user authentication and authorization using OAuth 2.0 and OIDC alongside Couchbase.

New and Improved Import in Couchbase Cloud
Discover the new Import feature in Couchbase Cloud that now enables Custom Key Generation, Configuration options, Key Preview, Cloud Storage and more.
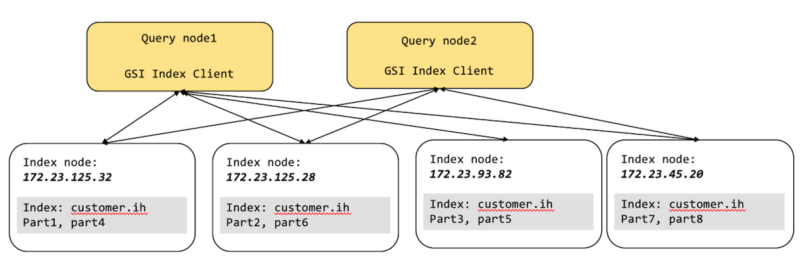
How to Use Global Secondary Index Partitioning for More Than Partitions
Learn how Global Secondary Index (GSI) partitions are useful for a variety of index management scenarios and use cases, including CQRS and more.

How to Take Python Input in Couchbase
Learn how to use Python for user input, when developing interactive, business-critical applications in Couchbase Server or Couchbase Cloud.

Why Data Encryption Is Essential
Data encryption can help organizations mitigate risks and stop data sprawl and cyberattacks before they occur. ✓ Do more with Couchbase.

Craft the Right Query, Get the Right Performance
Using Couchbases N1QL language, this blog will show you how you can iteratively craft performant queries alongside your Indexes

Upgrading Couchbase Community Edition
Upgrading Couchbase Community Edition to Enterprise Edition could be easily accomplished via rolling online upgrade process.

Use cases and Best Practices for Distributed Transactions through N1QL
Typical use cases and Best Practices for using the newly introduced distributed transactions through N1QL in Couhbase!What to do and what to avoid doing!?
Deep Dive on Multi-Factor Authentication
What is multi-factor authentication ? Why you should be using it and how to easily implement it with Couchbase Server.

Couchbase Support for Node-to-node Encryption
Couchbase supports node-to-node encryption or Cluster encryption by adding TLS based encryption to the connections between the nodes within a Couchbase cluster. When customers using Couchbase require us to comply with privacy regulations such as HIPAA (financial or healthcare customers...
Top Posts
- Data Modeling Explained: Conceptual, Physical, Logical
- What are Embedding Models? An Overview
- Data Analysis Methods: Qualitative vs. Quantitative Techniques
- What Is Data Analysis? Types, Methods, and Tools for Research
- Application Development Life Cycle (Phases and Management Models)
- Data Normalization vs. Denormalization Comparison
- App Development Costs (A Breakdown)
- What are Vector Embeddings?
- High Availability Architecture: Requirements & Best Practice...