Matching the needs of data governance with complex data management policies can be a daunting undertaking for enterprises. In this post, we demonstrate Couchbase Mobile’s ability to help implement enterprise data retention policies.
What is Data Governance?
According to NIST, Data Governance is “A set of processes that ensures that data assets are formally managed throughout the enterprise. A data governance model establishes authority and management and decision making parameters related to the data produced or managed by the enterprise”. In other words, data governance is a core element of data management and encompasses aspects of data privacy and security, integrity, consistency and usability. At a macro level, data governance policies control the flow of data across international borders. That’s a lot to chew on!
Needless to say, data governance has a vast purview. Data management scenarios are even more complex when managing distributed islands of data storage. In this post, we focus on a critical aspect of data governance related to the enforcement of data retention policies and show how Couchbase Mobile 3 facilitates the same.
Couchbase Mobile addresses several other data governance requirements such as data security and privacy to ensure that only authorized users have access to the relevant subset of data and that sensitive data never leaves the edge. Those aspects are not discussed in this post.
Sync Gateway access control model
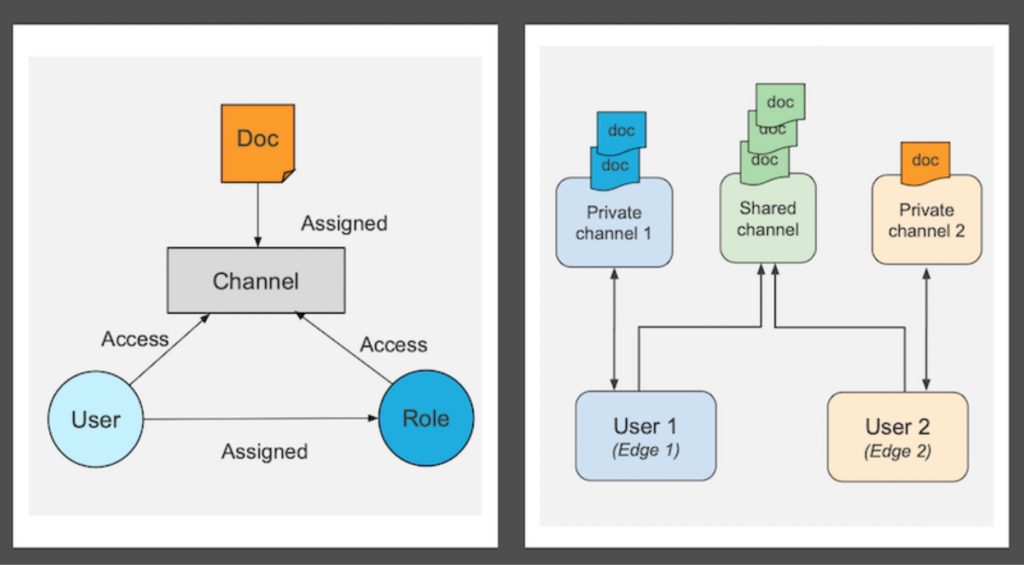
First, here is a quick primer on how Couchbase Sync Gateway access control works.
Granting Document Access
Every document in the system may be assigned to one or more channels. These channels can be user-defined or system-defined. Think of a channel as a tag associated with a document. A channel can have any number of documents, and an application can share a document across multiple channels.
A user, or a role, is a logical collection of users granted access to a channel. When gaining access to a channel, a user (or a role) is granted access to documents in the channel.
In the context of Couchbase Mobile, a user can be associated with an individual application user, a device, a store, a factory, a cruise ship, etc. It’s essentially the endpoint to which the data is synced.
A user can have access to multiple channels and multiple users can share a channel.
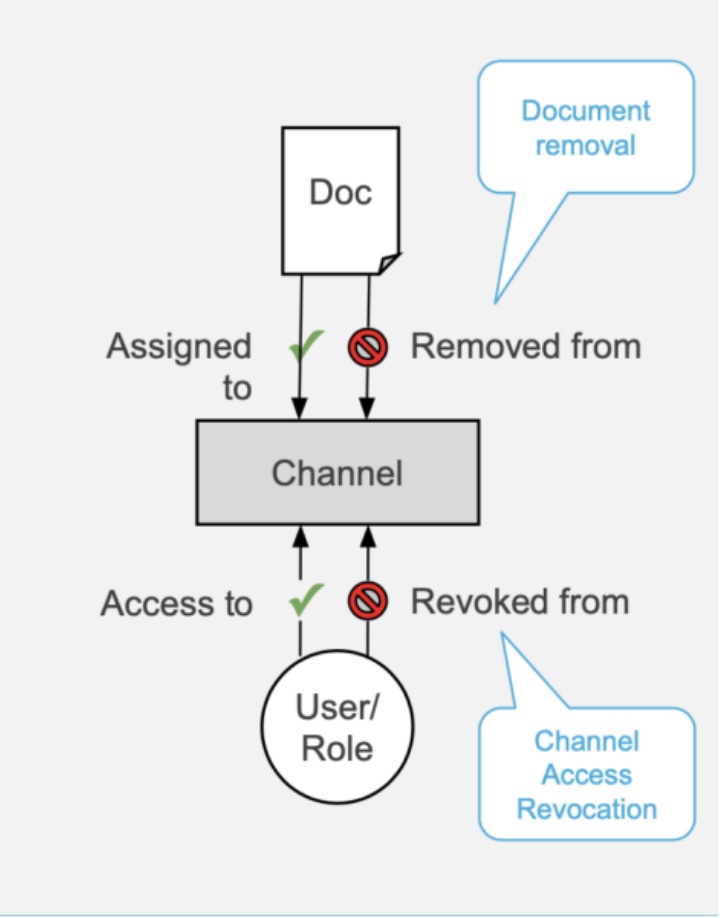
Revoking document access
A user can lose access to a document in two ways:
-
- When a document is removed from a channel, the user no longer has access to the document.
- When a user (or role) loses access to a channel, e.g., when channel access is revoked, the user loses access to all documents in the channel.
Data Retention use cases
Let’s take a look at a few examples that illustrate the data retention requirements related to data governance.
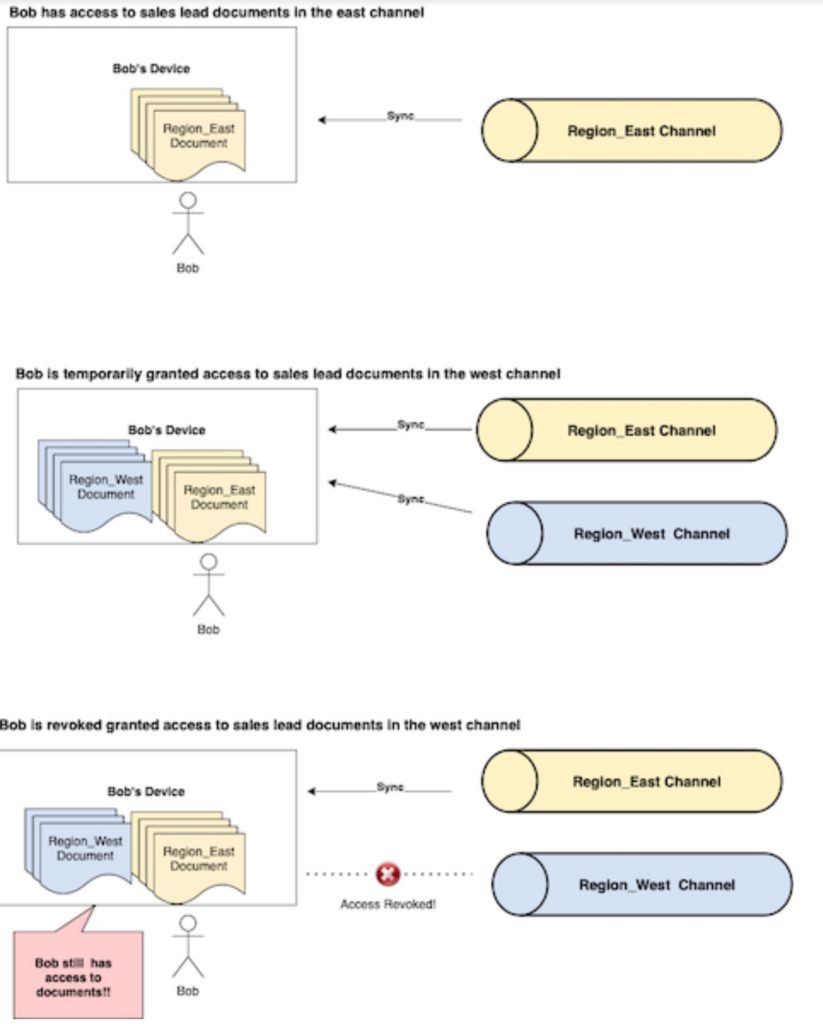
Enterprise sales teams
-
- A sales organization has one channel per sales associate. A channel includes region-specific lead documents.
- Bob, a sales associate in charge of Region_East, is temporarily granted access to the Region_West channel. Bob now has access to lead documents in Region_West and syncs them to his device.
- A new associate is hired to take over the West region and Bob should no longer have access to those leads. So access to the Region_West channel is revoked.
- Bob should also no longer have access to previously synced documents.
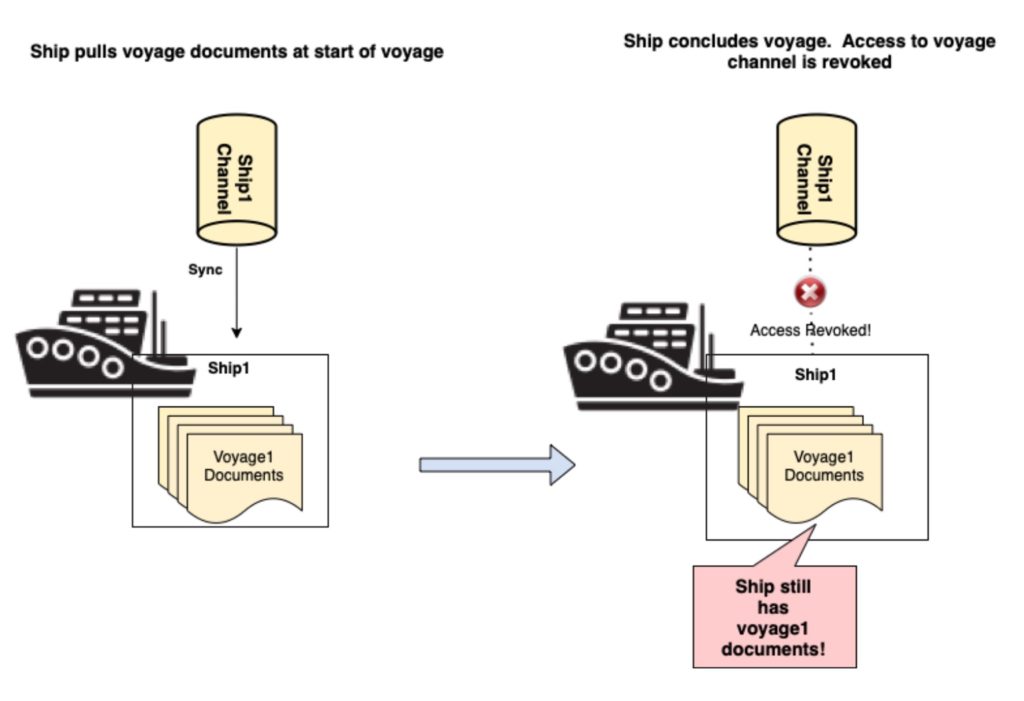
Cruise lines
-
- A cruise line treats each ship as an application user.
- At the start of the voyage, the ship is granted access to voyage documents that are pulled down from the backend systems in the cloud.
- At the completion of the voyage, the ship is revoked access to the voyage channel.
- Ships should no longer have access to the previously synced voyage documents.
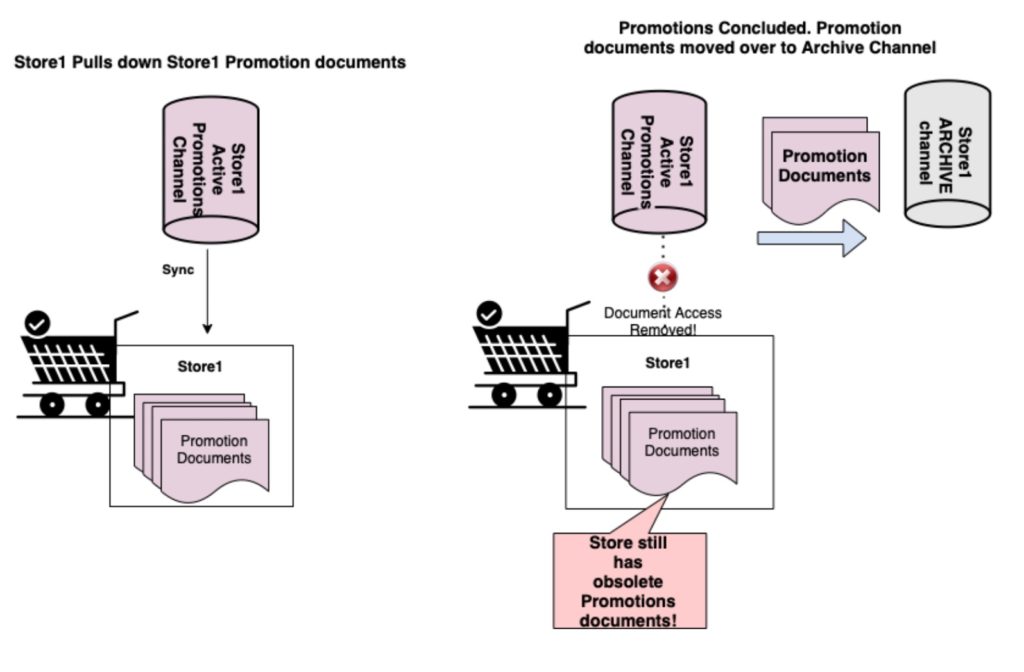
Retail store
-
- A retail organization has a channel per store. A channel includes documents specific to a store.
- A backend service creates store-targeted promotions and syncs them to each store
- Periodically, when the promotion is over, a backend process moves discontinued promotions from a store’s “active” channel to an “archive” channel.
- The store should no longer have the previously synced promotions that are now archived
Couchbase Mobile and data retention
In each of the distributed environments above, the requirement is that previously synced documents must be removed from the client. The enforcement of data retention policies and the guarantee that users can no longer access documents to which access is revoked is a cornerstone of data governance.
And this has to be supported regardless of whether the replication endpoint is Couchbase Lite or Sync Gateway.
Couchbase Lite client replication
When a Couchbase Lite user loses access to a document, either due to document removal or channel access revocation, the document is automatically purged from the user’s device! There is no additional business logic or code required on part of the user to enable this. So, considering the Enterprise Sales Org example above, as soon as Bob loses access to the Region_west channel, all the previously synced documents from that channel are automatically purged from his device. Therefore, guaranteeing that Bob no longer has access to unauthorized data.
Applications have the option of overriding this default behavior using a config option. Apps can also register for an Access Removed event that informs the app when the user has lost access to the document. This is shown in the code snippet below:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
// create replicator config var config = ReplicatorConfiguration.init(database: db, target: sgwUrl) config.enableAutoPurge = true // Override default auto purge behavior config.replicatorType = .pushAndPull // ... add other config options // create replicator _pushPullRepl = Replicator.init(config: config) _ = _pushPullRepl?.addDocumentReplicationListener({ (docRepl) in // Listen for Access Removed status notification }) _pushPullRepl?.start() |
Furthermore, in the case of channel access revocation (introduced in Couchbase Mobile 3), Sync Gateway identifies if the user has access to the document via some other channel. It then notifies Couchbase Lite of the document access removal if the document is not accessible via any of the user’s channels.
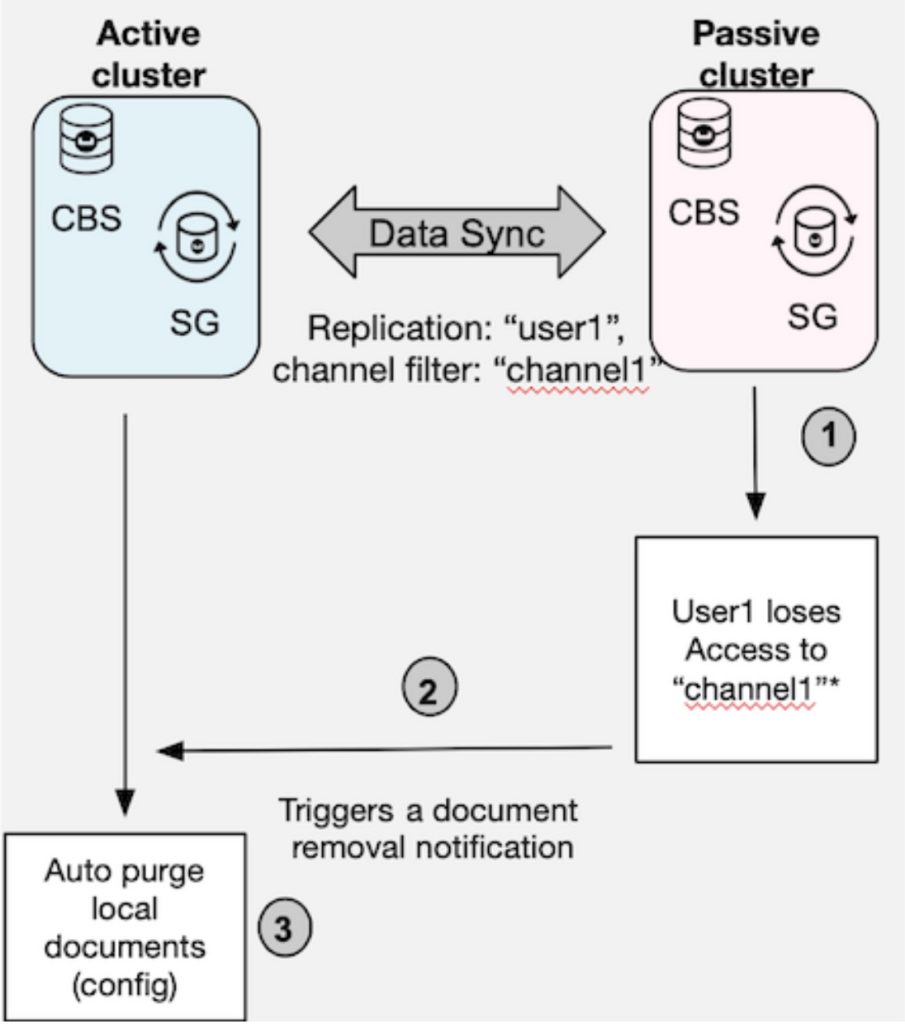
Inter-Sync Gateway replication
In the case of inter-Sync Gateway replication, when the replicating user on the target cluster loses access to a document, the active Sync Gateway cluster can be configured to auto-purge the document. For example, in the cruise ship use case, you would have replications set up between the ship and the shore—with the ship being the active cluster that initiates replications. When the voyage ends, the ship loses access to the channel and the voyage-specific documents are automatically purged from the ship.
Summary
In this post, we briefly discussed the importance of aligning data retention policies with data governance objectives. It is imperative that a data platform facilitate such compliance as it is an integral aspect of data management for all enterprises.
Couchbase Mobile’s out-of-the-box support for auto purging of local documents on access revocation guarantees that only authorized users retain access to documents. Likewise, the fine-grained access control, comprehensive data filters, encryption of data at rest and transit, authentication and authorization help to support other key aspects of data governance.
Next steps
Download Couchbase Mobile and try it for free. The documentation pages are an excellent resource for more information and the Couchbase Dev Forums are a great place to reach out to experts and other Couchbase developers.
If you have questions or feedback, please leave a comment below or feel free to reach out to me via Twitter or email.
Resources
The following resources are referenced in this post:
- NIST – Data Governance glossary
- Couchbase Mobile 3 – new advanced administration features (Blog post)
- Access control how-to in Sync Gateway (docs)
- Field-level encryption in Couchbase Lite (docs)
- Channel access revocation in Sync Gateway (docs)
- Couchbase Mobile – download link
- Couchbase Sync Gateway documentation
- Couchbase Developer Portal – Mobile apps
- Couchbase Developer Forums
Acknowledgment
I would like to thank Adam Fraser for his input on the blog post.